When thinking about network security, the focus often shifts to firewalls, encryption, and software solutions. Yet, physical security remains a foundational aspect of safeguarding networks. Threats like theft, hardware tampering, and unauthorized access can compromise sensitive data, disrupt operations, and lead to costly downtime.
In reality, a compromised server chassis or a swapped hard drive can instantly bypass expensive cybersecurity software. This article explores the critical blind spots in data center protection and how tamper-evident tools play a vital role in ensuring IT infrastructure safety.
The Hardware Blind Spot: Identifying Physical Threats in IT Environments
Physical threats to network infrastructure come in various forms. While natural disasters are a concern, the most immediate risk to data integrity comes from unauthorized human interaction. Unsecured doors, open server racks, and insufficient hardware monitoring create openings for threat actors to exploit.
Common physical security vulnerabilities in IT environments include:
- Lack of effective evidence-based access control measures at the individual server rack level.
- Inadequate monitoring for micro-intrusions, such as plugging an unauthorized USB device into an open server port.
- Poorly designed hardware transport protocols during equipment relocation or maintenance.
Unlike cyberattacks, many physical security threats can be executed with minimal technical expertise, making them a significant concern for organizations. For example, a person posing as a maintenance worker could easily gain access to critical equipment and clone a hard drive in minutes.
Addressing these vulnerabilities through robust physical security measures like restricted access, tamper-evident seals, and monitoring systems is crucial. Proactively identifying and mitigating these risks not only protects valuable assets but also ensures the integrity of business operations and prevents disruptions caused by physical breaches.
4 Essential Tamper-Evident Tools for Network Infrastructure
To safeguard the physical assets of your networks, IT managers must deploy specialized physical security layers. Here is how different tamper-evident tools protect specific network components:
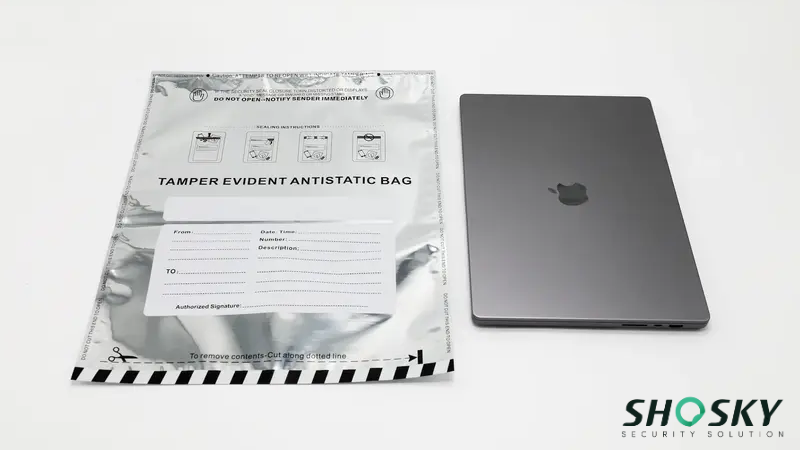
1. Tamper-Evident Bags for Asset Transport
Tamper-evident bags are specially designed to secure items like cash, documents, or sensitive equipment by showing clear evidence of unauthorized access. These bags feature security mechanisms such as adhesive closures, tamper-evident material, and hidden messages that reveal if the seal has been broken or compromised.
Use cases in IT environments of tamper-evident bags include:
- Securing confidential business documents and printed server access logs during transit.
- Protecting sensitive network components, such as hot-swappable hard drives or backup tapes, during transportation to off-site disaster recovery centers.
- Safeguarding encryption keys or offline storage devices to ensure accountability and an unbroken chain of custody.
By using tamper-evident bags, organizations can maintain the chain of custody for critical assets and detect any attempts at interference during equipment relocation.
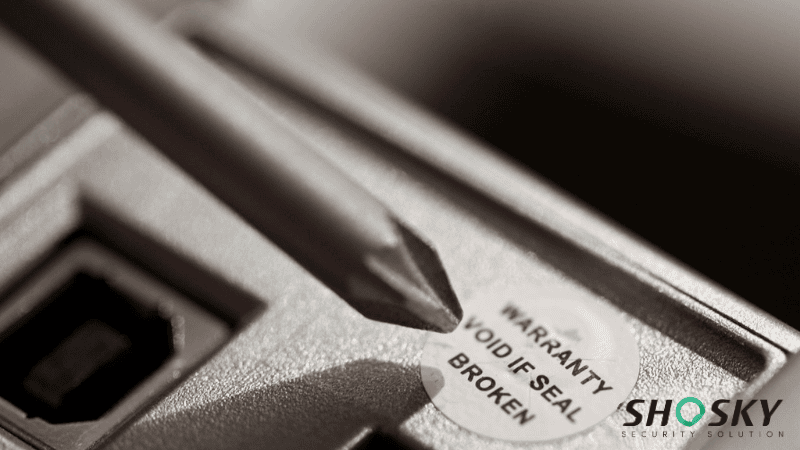
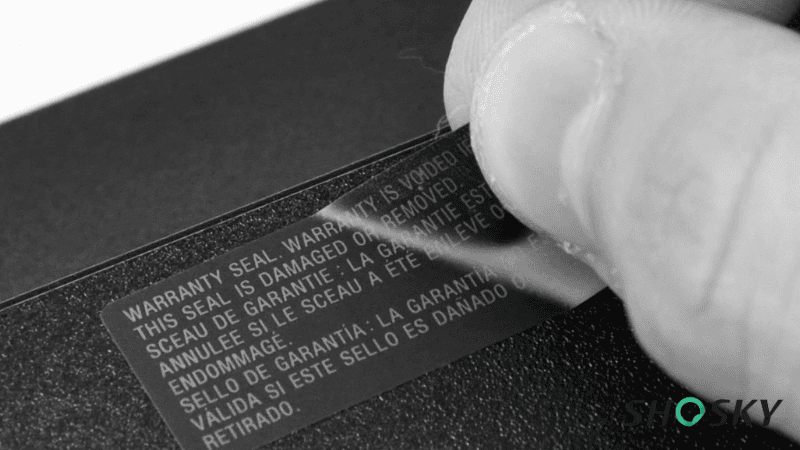
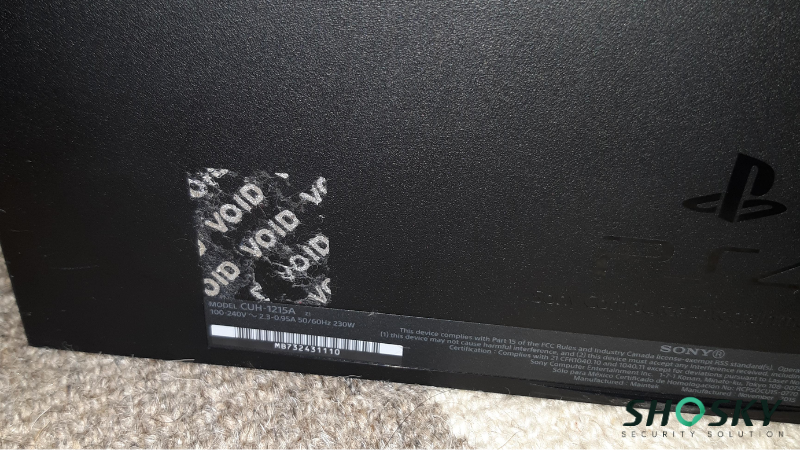
2. Security Labels for Hardware Integrity
Tamper-evident security labels are used to secure smaller but highly critical items like laptops, USB drives, server chassis, and network switches. These labels adhere to surfaces and display tamper evidence through broken patterns, color changes, or “VOID” residue when removed.
The key features and IT applications of security labels include:
- Port Blocking: Applying non-residue VOID labels over unused USB and Ethernet ports to prevent rogue device insertion (“BadUSB” attacks).
- Chassis Protection: Sealing server cases to ensure internal components like RAM and SSDs are not swapped or stolen.
- Smart Customization: Integrating company branding, serial numbers, or unique tracking codes for seamless synchronization with IT Asset Management (ITAM) software.
- Advanced Authentication: Embedding technologies like RFID chips or holographic designs to support high-level anti-counterfeiting and automated inventory audits.
The benefits of tamper-evident security labels extend beyond merely detecting tampering. They serve as a strong deterrent against unauthorized access and create a verifiable maintenance log for expensive IT hardware.
3. Tamper-Evident Seals for Data Centers
Tamper-evident seals are versatile security tools designed to protect network equipment, server racks, and other critical hardware. These seals create a physical barrier and show visible signs if tampered with between scheduled maintenance windows.
Types and applications of tamper-evident seals include:
- Cable Seals: Ideal for securing wiring and network cable systems to prevent unauthorized disconnections or tampering in high-traffic server rooms.
- Bolt Seals: Commonly used for locking data center racks or transport cases containing sensitive hardware. High-security seals, such as those meeting ISO 17712 standards, offer an added layer of traceability for cross-border transport.
- Plastic Security Seals: Suitable for managing access doors, server cages, or IT locker rooms where a quick visual tamper indicator is needed for routine audits.
High-security seals, such as numbered or barcoded seals, offer an added layer of protection by providing traceability. They are especially useful in environments where sensitive equipment is stored or transported, ensuring that unauthorized access is immediately identifiable.
4. Security Tapes for Equipment Shipping
Security tapes are a crucial component in securing shipments and network-related packages. These tapes use tamper-evident materials that leave visible marks or messages like “VOID” when removed. Customizable with logos, barcodes, or QR codes, they enhance both security and asset tracking.
Applications of security tapes include:
- Packaging critical network equipment for shipping to prevent supply chain theft or interception.
- Securing storage boxes containing spare hardware or archived data in shared colocation (Colo) data centers.
- Preventing unauthorized access to repair kits or emergency supplies. Once removed, the tape alerts receiving teams to reject the compromised shipment.
By incorporating security tapes into your packaging strategy, you not only deter tampering but also gain an added layer of accountability for global hardware deployment.
How to Choose the Right Security Solution for Network Hardware?
Selecting the right tamper-evident products is crucial to effectively securing network infrastructure.
The first consideration is the durability and reliability of the product. Given the nature of physical security threats, it’s crucial to choose tamper-evident seals, bags, barbed wires, and labels that can withstand wear and tear.
For IT hardware, environmental factors are critical. Labels applied to the server chassis must withstand continuous heat without peeling. High-tack PET materials are highly recommended for warm server rooms. For frequent maintenance areas, use non-residue VOID labels that show tampering but don’t leave sticky glue on expensive switchboards.
It’s also important to choose tamper-evident products that comply with industry standards. Compliance with recognized standards ensures that the products meet the necessary legal and security requirements. It also ensures that the security measures are aligned with best practices, offering effective protection against emerging threats.
Standards from authorities such as ISO 17712 (high security seals) and ISO/IEC 27001 (IT security management) can serve as guidelines for selecting products that align with the organization’s security goals.
By carefully evaluating these factors, organizations can select tamper-evident tools that provide comprehensive protection for their physical network infrastructure while enhancing the overall security posture against potential threats.
Common Mistakes in Physical IT Security (And How to Avoid Them)
Even with strong intentions, many organizations unknowingly leave their physical networks vulnerable. Identifying and addressing these common missteps is key to strengthening your overall security posture. The table below outlines frequent mistakes and their associated risks:
| Mistake | Why It’s a Problem | Recommended Solution |
|---|---|---|
| Ignoring small access points | Minor oversights like unsealed cabinets can be exploited by intruders. | Use tamper-evident seals and perform regular physical inspections. |
| Over-reliance on digital security | Physical breaches can bypass all software-based protections. | Integrate tamper-evident tools with digital security protocols. |
| Lack of employee training | Staff unaware of protocols may unintentionally compromise physical security. | Conduct regular training and establish clear procedures for physical asset handling. |
| Infrequent audits of physical defenses | Outdated or damaged seals may fail to reveal tampering. | Implement routine audits to check the integrity of tamper-evident devices. |
| Poor access control implementation | Unrestricted access increases the risk of insider or outsider threats. | Restrict access to sensitive areas with biometrics, keycards, and surveillance systems. |
By avoiding these pitfalls and taking a proactive approach, organizations can drastically reduce the likelihood of physical breaches. Consistent evaluations, staff training, and tamper-evident measures work together to form a reliable line of defense.
Future Trends: Merging Physical and Cybersecurity
As technology advances, innovations in tamper-evident products are set to revolutionize physical network security. New materials and designs are being developed to offer enhanced durability, improved functionality, and even more effective detection of tampering attempts.
For instance, the integration of RFID chips with tamper-evident bags or seals could provide real-time alerts to network administrators, making it easier to respond to physical security breaches as they occur. Such innovations will undoubtedly make it even harder for attackers to bypass security measures undetected.
Besides, a growing trend in physical network security is the integration of physical and cybersecurity solutions into a hybrid model. This approach combines the strengths of both domains, allowing for a more comprehensive defense against both digital and physical threats.
By merging both elements, organizations can create a robust security framework that is better equipped to handle potential threats and mitigate vulnerabilities across their entire network system.
FAQs
Q1: Are there standards for tamper-evident products in IT security?
Yes, tamper-evident products in IT security must comply with industry standards such as ISO/IEC 27001.
Q2: What is a tamper-evident bag used for in network security?
A tamper-evident bag is used to securely transport sensitive equipment, such as backup hard drives, offline storage media, or printed access logs, protecting them from unauthorized access or undetected tampering during transit.
Q3: How do security labels protect network ports?
Specialized non-residue VOID labels can be placed over open USB or Ethernet ports on servers. If someone attempts to plug in an unauthorized device, the label reveals a “VOID” message, instantly alerting administrators to the physical breach.
Conclusion
Ensuring the physical security of IT infrastructure is vital to protecting sensitive data and maintaining uninterrupted operations. Tamper-evident solutions, such as seals, bags, and labels, act as a strong deterrent against tampering and unauthorized access. Incorporate these tools to reduce risks, stay compliant, and protect assets effectively.
Protect Your IT Assets with Shosky Security
At Shosky Security, we specialize in providing top-notch tamper-evident bags, seals, and labels. Whether it’s securing network hardware or ensuring the integrity of critical assets, our solutions help safeguard your operations with confidence. Contact us today to explore how we can enhance your network’s physical security.