Every investigation relies on a secure chain of custody to maintain the integrity of its evidence. Whether it is a criminal case involving DNA or a corporate audit regarding financial fraud, the physical security of the evidence is paramount. Without proper tools and protocols, evidence can be compromised, leading to inadmissibility in court and the failure of the entire case.
This guide serves as a comprehensive resource for law enforcement officers, evidence custodians, and forensic professionals. We will cover the essential tamper-evident tools, detailed procedural steps, and the critical environmental factors necessary to manage evidence from the crime scene to the courtroom.
Why Chain of Custody Integrity is Non-Negotiable?
The chain of custody is the chronological documentation that records the sequence of custody, control, transfer, analysis, and disposition of physical or electronic evidence.
Its primary purpose is to authenticate the evidence. It proves that the item presented in court is the exact same item collected at the scene and that it has not been altered, substituted, or contaminated.
If the chain is broken, the evidence may be excluded under the legal doctrine often referred to as the “fruit of the poisonous tree.” This means that if the source evidence is tainted due to poor handling, any subsequent discoveries derived from it are also inadmissible.
Resources like the Cornell Law School Legal Information Institute emphasize that the prosecution bears the burden of proving the chain remains intact.
Beyond the courtroom, poor chain-of-custody procedures create operational liabilities.
- Contamination: Biological evidence degrades if sealed improperly.
- Theft: High-value evidence like narcotics or cash is vulnerable to internal theft if seals are not serialized and tracked.
- Liability: Agencies face lawsuits and loss of public trust when evidence goes missing.
The consequences of breaches in the chain of custody can be severe, with the potential to impact the outcome of legal proceedings and erode public trust in the judicial system. High-profile cases, such as the O.J. Simpson trial and the Rodney King case, have demonstrated how mishandling of evidence can lead to acquittals or case dismissals, undermining the pursuit of justice.
Now that we understand the gravity of the process, we must look at the physical hardware required to secure these items effectively.
Essential Tamper-Evident Tools for Securing Evidence
When it comes to maintaining an unbroken chain of custody, a variety of tamper-evident tools are available. Here are a few of the essential ones:
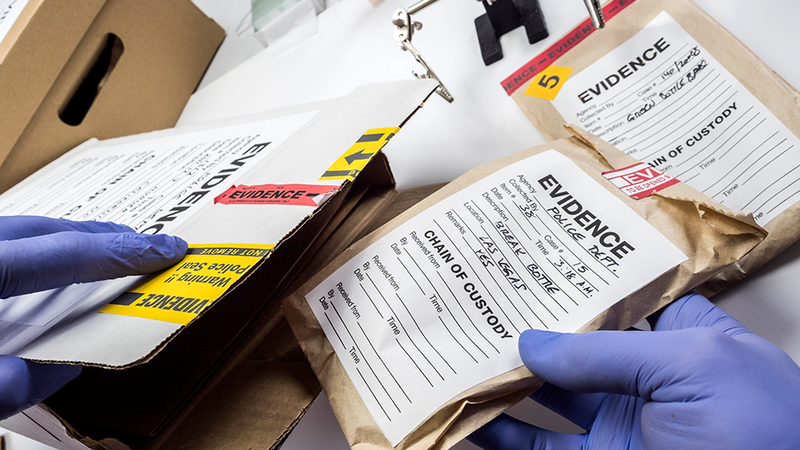
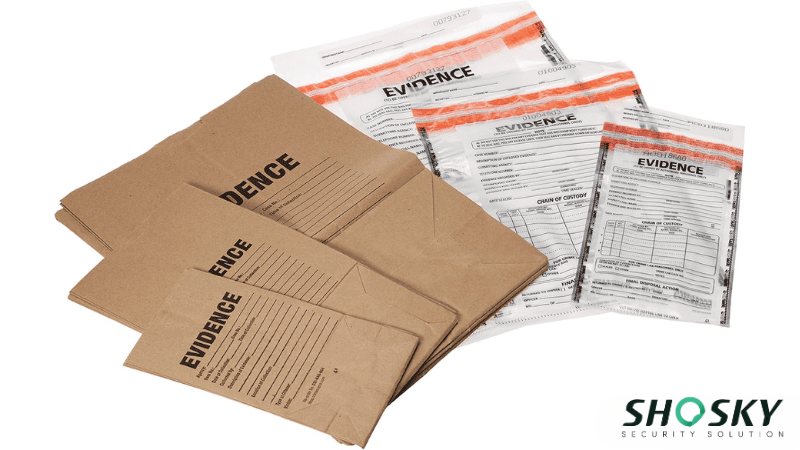
Tamper-Evident Bags
Ensuring evidence security starts with reliable tamper-evident bags. Tamper-evident bags are storage solutions designed to provide visual evidence of unauthorized access or tampering.
Their primary function is to ensure the integrity and security of their contents, offering a clear indication if someone has attempted to open or compromise the package. This is crucial in such cases where custody issues can arise, and maintaining the integrity of the contents is paramount.
The most common types of tamper-evident bags include plastic tamper-evident bags, paper tamper-evident bags, and reusable tamper-evident bags:
- Plastic Tamper-Evident Bags: These are the most commonly used type and are made from durable plastic materials. They often feature heat-sealed seams, which are designed to break if tampered with, providing records of any unauthorized access.
- Paper Tamper-Evident Bags: These bags are used when evidence needs to be sealed in a more environmentally friendly or discreet manner. Paper bags often have adhesive seals that show clear signs of tampering.
- Reusable Tamper-Evident Bags: These bags can be used multiple times without compromising the security of the collected items. They are made from heavy-duty materials and feature specialized sealing mechanisms that ensure the bag can be resealed after use without risk of contamination.
Tamper-evident bags are equipped with several key features to ensure evidence security. These bags include different security seal types, such as adhesive seals, zipper closures, and heat seals, that break when tampered with, providing clear signs of unauthorized access.
Many bags also feature unique serial numbers for tracking purposes, ensuring each piece of record can be individually identified and linked to a specific case. Additionally, the bags are made from tear-resistant materials, which makes them harder to open without leaving visible evidence of tampering, thus further securing the contents inside.
This attention to detail is crucial in proving the identity and legitimacy of the evidence in court.
Tamper-Evident Bag Tape
While tamper-evident bags are essential for protecting evidence, ensuring the bags are properly documented with accurate tamper-evident bag tape is equally important. Tamper-evident bag tapes contain vital information about the case, evidence, and individuals involved in the collection process.
Proper labeling ensures accountability, minimizes the risk of errors, and provides a clear timeline of the evidence’s journey from collection to court.
The information that should be included on a tamper-evident bag tape includes:
- Case ID: This unique identifier ties the evidence to a specific case, ensuring that the evidence can be matched with its corresponding case file.
- Collector’s Name: The name or identity of the person involved in evidence gathering must be included to maintain accountability and prevent disputes about who handled the evidence.
- Date and Time: Documenting the exact date and time of collection is critical for maintaining an accurate timeline of the evidence’s handling.
The placement of the label on the evidence bag is just as significant as the information it contains. Labels should be adhered securely in a visible location that does not interfere with the bag’s tampering seals. This placement ensures the label remains intact throughout the chain of custody, even when stored in a secure place or under controlled security conditions.
Comprehensive labeling plays a crucial role in the investigation process. It helps prevent tampering, avoids errors, and ensures the evidence’s journey is properly documented from initial possession to court testimony. By enabling investigators, lawyers, and the jury to track evidence effectively, accurate labeling supports the efforts to convict persons and uphold justice.
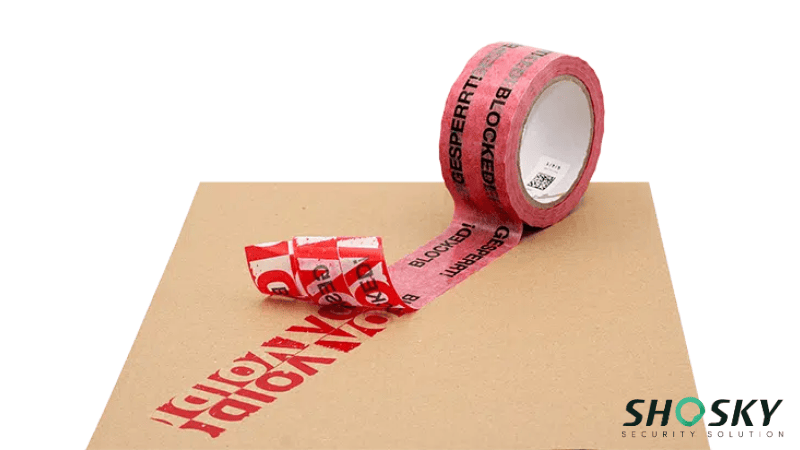
Tamper-Evident Tape
Tamper-evident security tape is an essential tool for sealing packages, evidence boxes, and storage containers. Its main purpose is to reveal any attempt to tamper with a sealed item. When someone tries to lift or peel the tape, it leaves visible signs. These may include a hidden message like “VOID” or “OPENED,” damage to the surface, or a color change. These features serve as a visual warning.
Security tape strengthens the protection of bags, envelopes, cartons, and similar items. Once applied, it bonds firmly to the surface. It cannot be removed or repositioned without showing signs of interference. This is critical when transporting or storing sensitive materials or high-value goods.
Common features of security tape include:
- Tamper-Reveal Messages: Words or symbols appear if the tape is disturbed.
- Sequential Numbering: Matches sealed items to their records.
- Custom Printing: Barcodes, logos, or case IDs can be printed in advance.
- Material Options: Available in destructible vinyl, film, or paper for different applications.
Security tape is often used on document pouches, evidence containers, and equipment panels. It helps verify authenticity during inspections. It also works well with other tamper-evident tools, such as bag seals or RFID tags.
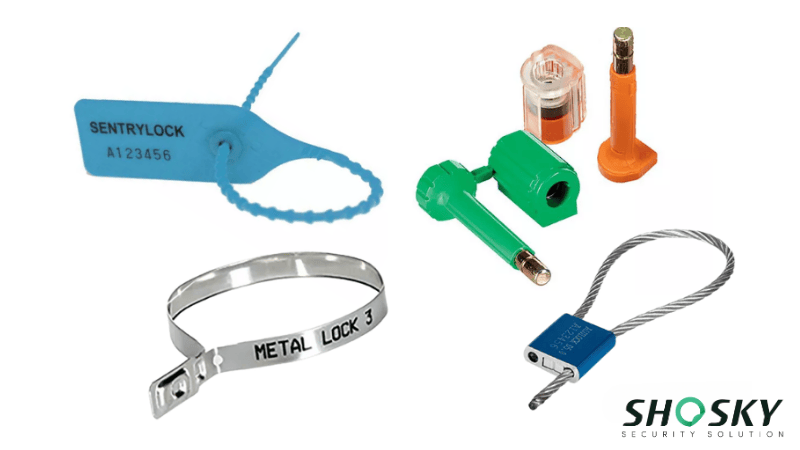
Tamper-Evident Seals
Security seals are locking devices that protect containers, doors, cabinets, or bags from unauthorized access. Once applied, these seals must be broken or damaged to open the item.
Each type of seal is designed for specific levels of security:
- Plastic Pull-Tight Seals: Adjustable and disposable. Ideal for bags and totes.
- Bolt and Cable Seals: Strong and tamper-resistant. Used on freight and shipping containers.
- Metal Strap Seals: More durable than plastic. Used when extra strength is needed.
- Twist or Wire Seals: Common in meter reading and law enforcement.
Security seals often include the following features:
- Unique Serial Numbers: Prevent replacement and support inventory tracking.
- Barcodes or QR Codes: Allow digital scanning and monitoring.
- Color-Coding: Helps with sorting and identification.
In chain-of-custody processes, security seals act as control points. They show whether an item was accessed between transfers. Their low cost, simplicity, and visibility make them a reliable choice across industries like law enforcement, logistics, retail, and legal services.
Other Tools and Technologies for the chain of custody
In addition to tamper-evident solutions, there are several other tools and technologies available to support chain of custody issues.
RFID Technology
Radio Frequency Identification (RFID) provides wireless tracking of items using digital tags. Each tag has a unique identifier. These tags are often placed inside tamper-evident bags or secured storage containers. RFID technology offers real-time updates on item location. It reduces the need for manual handling and increases accuracy.
RFID systems also create automatic records. Every scan or interaction is logged. This helps maintain transparency and ensures full accountability. Organizations use RFID to manage large amounts of evidence or materials. It improves search times, reduces human error, and supports efficient workflows.
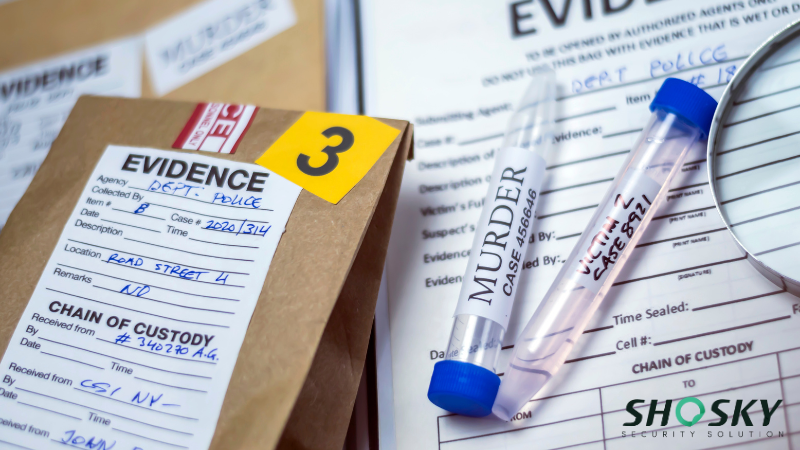
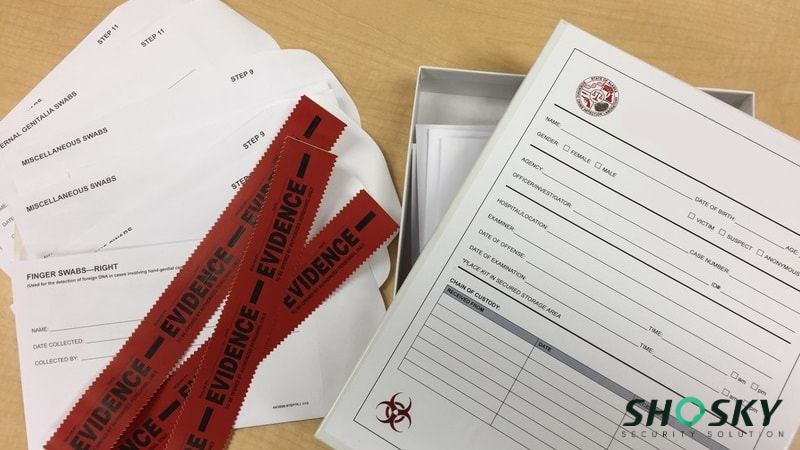
Chain-of-Custody Forms
For the prosecution in criminal cases, having a fully completed and accurate chain of custody form is crucial to address any legal challenges regarding the authenticity of the evidence. Chain-of-custody forms are used to document every interaction with the evidence, from collection through to courtroom presentation.
These forms provide a written record of the evidence’s journey, which is crucial for ensuring transparency and accountability. They typically include sections for the collector’s name, date, time, storage location, and the signature of each individual who handles the evidence.
Digital Evidence Tracking Systems
According to the National Institute of Justice (NIJ), digital evidence is latent and can be easily altered or destroyed. So you need some special solutions to protect your evidence, like:
- Faraday Protection: Mobile devices should be placed in Faraday bags immediately. These bags block radio signals, preventing the device from receiving a “remote wipe” command or connecting to a network, which could alter the data timestamps.
- Write Blockers: When analyzing digital media, forensic experts use hardware “write blockers.” These devices ensure that when a hard drive is plugged in for analysis, the computer can read the data but cannot write any new data to the drive, preserving the original state.
These systems are increasingly used in place of paper-based systems, providing greater efficiency, security, and accessibility for law enforcement agencies.
Different types of evidence react differently to packaging materials. Using the wrong bag can be just as damaging as breaking a seal. To help you select the right packaging for your specific needs, we have compiled a quick reference guide:
| Evidence Type | Recommended Packaging | Why? |
|---|---|---|
| Narcotics (Dry) | Plastic Tamper-Evident Bag | Prevents loss of powder; protects from external moisture; durable. |
| Currency / Cash | Plastic Tamper-Evident Bag | Transparent allows counting without opening; high security seal prevents theft. |
| Bloody Clothing (Wet) | Paper Evidence Bag | Breathable material allows moisture to escape, preventing mold and DNA degradation. |
| Smartphones / Tablets | Faraday (Anti-Static) Bag | Blocks remote wiping signals; protects circuitry from static shock. |
| Guns / Knives | Cardboard Box (with zip ties) | Rigid packaging prevents the weapon from cutting through the bag and injuring handlers. |
| Trace Evidence (Hair/Fiber) | Pharmaceutical Fold / Envelope | Prevents tiny particles from being lost in the corners of a large bag. |
Step-by-Step Guide to Maintain Chain of Custody
As we discussed above, maintaining an unbroken chain of custody is essential to ensure the integrity and admissibility of evidence in legal proceedings. Now, here is a step-by-step guide to maintaining the chain of custody throughout the evidence-handling process.
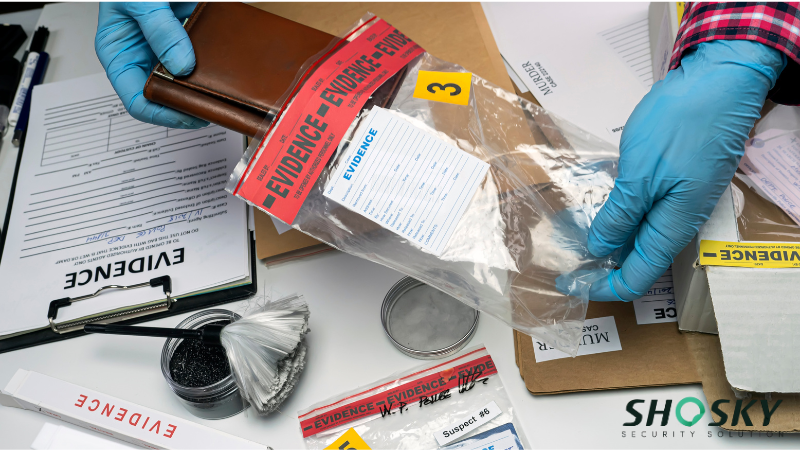
Step 1: Evidence Collection
The foundation of a strong chain of custody begins at the point of evidence collection. Proper handling techniques are essential to avoid contamination or alteration of the evidence. Investigators must use appropriate tools and follow established protocols to gather and package each item securely.
Ideally, place only one item per bag. This prevents items from contaminating each other. Sharps, such as knives or syringes, should be placed in rigid “sharps containers” or cardboard tubes before being placed in a bag to prevent injury to the evidence clerk.
When collecting evidence, it should be placed immediately into tamper-evident bags. These specialized containers visibly indicate any unauthorized access, providing a clear record of the evidence’s integrity. Accurately completing the evidence bag labels is also crucial at this stage, documenting the case details, the collector’s name, date, and time of collection.
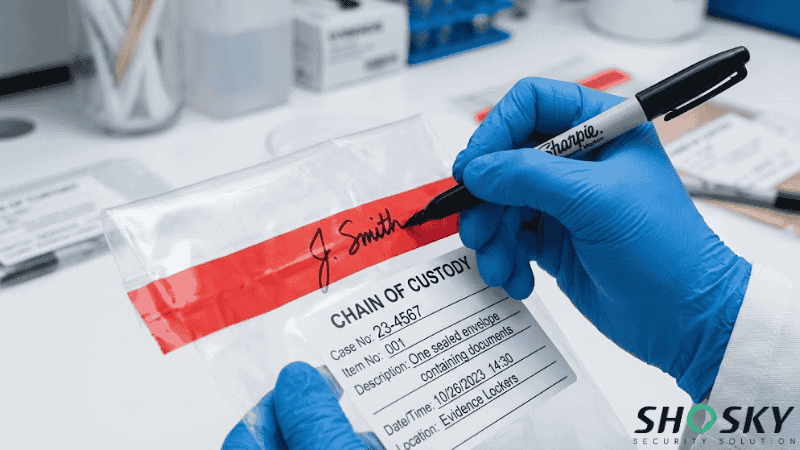
Step 2: Evidence Sealing
Proper sealing is the most critical physical step. Here are the sealing ways of some standard tamper-evident tools:
- Plastic Bags: Remove the release liner from the tamper-evident adhesive strip. Press the seal down firmly from the center outwards to remove air bubbles. Ensure there are no creases or gaps where a probe could enter.
- Paper Bags: Fold the top of the bag down twice. Apply evidence tape across the entire opening, extending the tape down the sides of the bag.
After sealing, the collector must sign their name and record the required data, including case number, item number, description, date/time, and location. The signature should start on the bag, go over the tape, and end on the bag again. This makes it impossible to remove and replace the tape without breaking the signature line.
In addition, record the required data, including case number, item number, description, date/time, location, and collector name.
Step 3: Evidence Storage
After collection, the evidence must be stored in a secure location that maintains its integrity. Choosing the appropriate storage facility is key, with considerations given to factors like access control, environmental conditions, and monitoring systems. Restricted-access evidence rooms or specialized storage containers can help prevent unauthorized entry and ensure the continued safety of the evidence.
In addition, the environmental conditions for storing evidence are also essential, as they are a point to prevent evidence from being destroyed internally. Here are some examples:
- Biological Evidence
Biological evidence, such as DNA, is highly perishable and must be stored under strict temperature control to prevent degradation. Liquid blood and urine kits require refrigeration between 2°C and 8°C, while long-term preservation of DNA samples typically requires freezing at -20°C.
If power fails or a freezer malfunctions, the evidence can be compromised, so secure storage facilities must maintain continuous temperature monitoring logs as part of the chain-of-custody documentation.
- Narcotics and Chemicals
Chemicals can be volatile. Drugs like marijuana can mold if stored in plastic without drying. Other chemicals may degrade in heat. Ventilation and humidity control are essential components of the storage facility.
- Digital Media Storage
Hard drives and magnetic tapes are sensitive to temperature extremes and magnetic fields. They should be stored in climate-controlled environments (around 18-22°C) with low humidity to prevent corrosion of the internal components.
Step 4: Evidence Transfer
When the evidence needs to be moved between locations or handed off to different parties, such as law enforcement, forensic teams, or legal professionals, the chain of custody must be carefully documented.
Before recording the transfer record, the person receiving the evidence must visually inspect the bag. Is the seal intact? Does the label match the log?
After that, both parties must sign and date the Chain of Custody form, recording the exact time. The evidence is then stored in a secure, access-controlled room.
Pay attention, standardized protocols for evidence transfer should be followed, including the use of tamper-evident seals on transportation containers and the completion of comprehensive chain-of-custody forms.
The chain-of-custody forms provide a detailed record of the evidence’s journey, including the names of individuals involved, the dates and times of each transfer, and the reasons for the movement. This documentation ensures a clear and unbroken trail of custody, minimizing the risk of evidence tampering or mishandling.
Step 5: Court Presentation or Final Disposition
When the time comes to present the evidence in court or dispose of it after the case’s conclusion, the chain of custody must be maintained until the very end.
Investigators must demonstrate that the evidence has remained intact and unaltered throughout the entire process, from collection to the courtroom or final disposition.
During court presentations, the handling history and documentation of the chain of custody will be scrutinized. That’s why meticulous record-keeping and the ability to account for every step of the evidence’s journey are essential to upholding its credibility and admissibility.
After the case is closed, the final documentation, including the resolution of the chain of custody, must be carefully recorded and preserved for potential future reference or legal proceedings.
Best Practices to Avoid Chain of Custody Failures
To maintain a robust chain of custody that withstands cross-examination, agencies should adhere to these best practices.
1. Limit the Number of Handlers
Every time evidence is transferred, the risk of error increases. Keep the chain as short as possible. If Officer A collects it, they should ideally be the one to deposit it into the evidence locker.
2. Photograph Everything
Photos should be taken of the evidence in situ, of the evidence after it is bagged, and of the seal itself. These photos become part of the case file and provide visual proof that the packaging was correct at the time of collection.
3. Never Pre-Sign Seals
Never sign a seal tape before it is applied to the bag. The signature must cross over the edge of the tape onto the bag to be effective as a security measure.
4. Conduct Random Audits
Do not wait for a trial to check your evidence room. Supervisors should conduct random spot checks. Pull a random case file and ask to see the corresponding evidence. Check that the location in the log matches the physical location and that the seals are intact.
5. Use Certified Supplies
Do not use generic sandwich bags or office tape. Defense attorneys know to look for this. Use certified tamper-evident supplies that meet industry standards. This demonstrates professionalism and adherence to protocol.
FAQs
Q1: What is the correct order for the chain of custody?
The correct order for the chain of custody involves evidence collection, evidence storage, evidence transfer, and court presentation (with full documentation).
Q2: Are digital chain-of-custody systems reliable for court use?
Yes, digital chain-of-custody systems are reliable for court use as long as they are properly implemented and maintain full audit trails.
Q3: What causes a broken chain of custody?
A chain breaks when evidence is mishandled, poorly documented, improperly sealed, or transferred without accurate records.
Q4: How can agencies reduce chain-of-custody errors?
They can reduce errors by using certified security supplies, limiting handlers, photographing seals, and conducting regular audits.
Q5: Who is responsible for maintaining the chain of custody?
Any individual who handles the evidence is responsible for documenting and preserving its integrity.
Conclusion
A well-managed chain of custody is critical to maintaining the integrity of evidence in legal proceedings. The use of bags, labels, RFID tags, and other security tools provides transparency, efficiency, and accountability throughout the evidence-handling process to manage a secure chain of custody. By implementing robust security solutions, you ensure that evidence remains protected and trusted from collection to presentation in court.
Maintain a Foolproof Chain of Custody
To ensure your evidence management system is foolproof, consider Shosky Security’s range of tamper-evident solutions. Our products help you safeguard the integrity of your evidence throughout its journey. Contact us to learn more about our customized security solutions and protect your evidence with the highest level of reliability and transparency!