Counterfeit products critically damage brand equity and pose severe risks to consumer safety, resulting in massive revenue attrition for global manufacturers. In today’s highly vulnerable supply chains, standard packaging protection is no longer sufficient. It has transitioned from a simple competitive advantage to an absolute operational necessity.
This guide explores how industrial security printing helps brand protection teams and packaging engineers implement uncompromising anti-counterfeit measures.
The Power of Layered Defense: Overt and Covert Security
Effective counterfeit packaging prevention is never built on a single solution. Responsible packaging professionals employ a multi-layered security system to deter sophisticated fraud operations:
- Overt Features: Visible to the naked eye for initial defense. They allow consumers and retail inspectors to verify authenticity instantly without specialized scanning devices.
- Covert Features: Concealed elements requiring forensic tools like UV lights or scanners. They enable unobtrusive field validations by investigators without alerting counterfeiters.
A combination of the two results in a system that is hard to duplicate and easy to confirm, which is a vital element in contemporary brand protection strategies. The anti-counterfeit packaging market has already achieved the milestone of about 126 billion dollars in 2023 and is projected to increase substantially with the increasing cases of counterfeit, especially in the pharmaceutical and food product sectors.
7 Advanced Security Printing Techniques for Anti-Counterfeit Packaging
Deploying industrial security printing methods physically prevents the unauthorized replication of product packaging. Procurement teams should evaluate the following seven highly engineered techniques:
1. Micro Text Printing
Microtext printing is the process of printing the text in such a small size that it appears as a single line or a border. The hidden text is only readable under magnification. Ordinary commercial printers do not have sufficient precision to accurately reproduce microtext.
Security Advantage:
Micro printing becomes illegible and blurred when it is scanned and duplicated by counterfeiters. This makes it a very cost-effective method of anti-counterfeiting technologies, particularly in health, pharmaceutical, and luxury packaging, where minute detail is crucial.
Microtext is widely applied to labels, folding cartons, security seals, and blister packaging, and thus it can be highly scalable across various packaging formats. It also facilitates regulatory compliance in highly regulated industries.
2. UV Invisible Ink
UV Invisible ink is completely invisible to normal light, but it is visible when exposed to a certain UV wavelength. This technique is effective in covert security features that are discrete.
Security Advantage:
Teams that protect brands can ensure authenticity in real time. The fact that counterfeiters usually do not know about these hidden traces means that UV ink gives an extra line of unseen protection along the supply chain.
UV ink is extensively applied in the working conditions of warehouse verification, distribution checkpoints, and customs inspections, and it allows fast authentication without interfering with working processes.
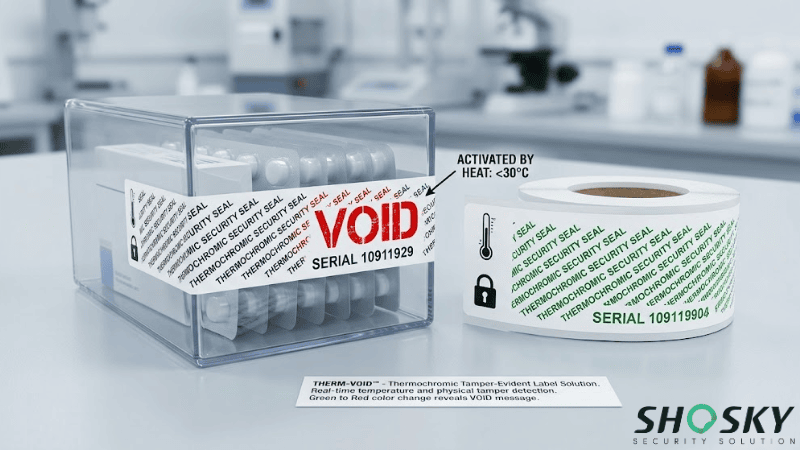
3. Thermochromic Ink
Thermochromic ink is a color-changing or disappearing ink that reacts when subjected to specific temperatures, e.g., body heat or cold. This is what allows immediate and interactive consumer authentication.
Security Advantage:
Thermochromic pigments have supply chains tightly controlled by industrial manufacturers, so that counterfeiters are unable to source these materials through normal channels. This scarcity forms a natural lockout: without the proper pigments, the process is halted at the material stage before any printing equipment ever appears.
For brands, this represents a security layer protected upstream, not necessarily at the printing stage.
4. Guilloche Patterns
Guilloche patterns are decorative geometric designs based on mathematical formulae. You can find this kind of design on banknotes, passports, etc.
Security Advantage:
You cannot create replicas of these artworks with conventional design software or scanning devices. Even a slight mistake can be detected.
The complexity and precision of guilloche patterns make them a strategic choice by high-security industries, including the printing of currency, government documents, and high-quality brand packaging.
5. Variable Data Printing
Variable data printing assigns a unique identifier (a QR code, serial number, barcode, etc.) to each unit of the product, essentially making each package a unique, traceable object. This is achievable by means of serialization, where each of the codes is produced separately and registered in a centralized database in the cloud at the point of production.
Security Advantage:
The real enforcement power of this technique is database verification. Each scan creates a live check with the master record. A counterfeiter who copies a single QR code into thousands of units will, unwillingly, create multiple hits on the same database record.
The system will pick this up immediately, isolate the anomaly, and allow a quick, accurate response before the fake product moves further along the chain.
6. Color Shifting Inks
Color-changing inks contain tiny metal flakes that vary in color depending on the viewing angle. These inks cannot be replicated by standard CMYK printing processes.
Security Advantage:
They provide a clear and premium authentication method that consumers can easily recognize, making it an effective visible security feature in anti-counterfeit packaging.
They are also extremely hard to imitate visually, since their intricate designs act as a strong deterrent to counterfeiters who lack access to specialized ink formulations.
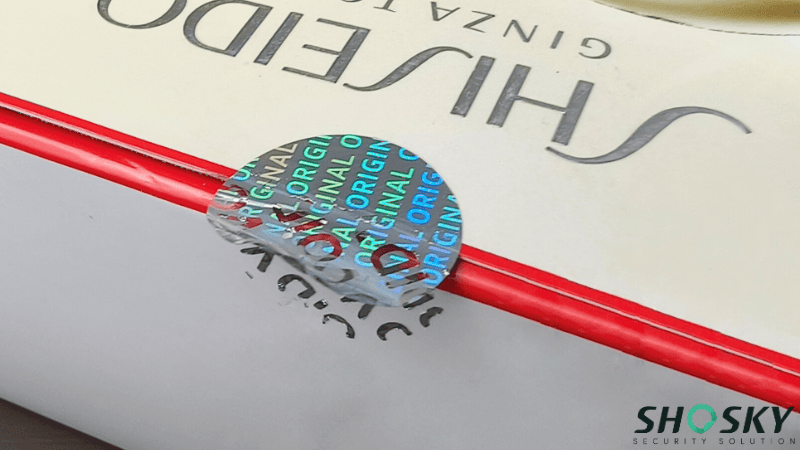
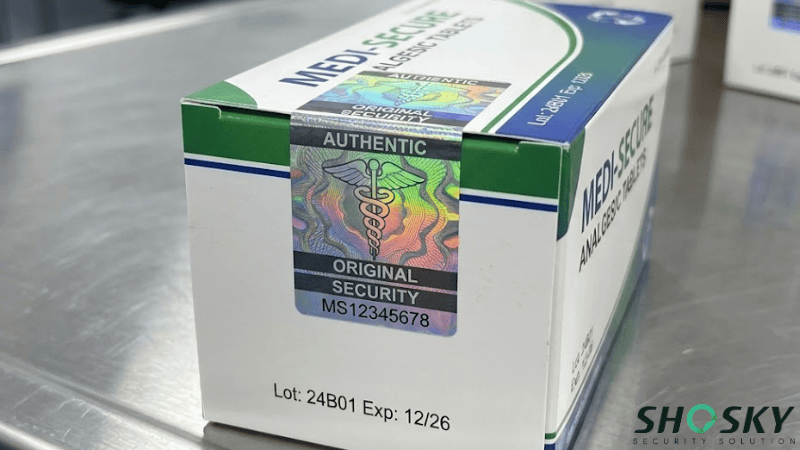
7. Holographic Hot Stamping
This method inserts a custom holographic image into the packaging material under pressure and heat. Security holograms cannot be scanned or photocopied like printed graphics.
Security Advantage:
Custom holograms are exclusive in branding and a good visual deterrent. They are especially efficient in sectors where the authenticity of products is of high importance to consumer confidence.
Personalized holograms can be used as a potent visual deterrent and a branding feature. The visual qualities of each hologram can be designed to be specific to a brand or product line, and duplicating them is made exceptionally hard. They do this especially well in industries where consumer trust in the authenticity of the product is directly related to their purchasing behavior.
To help procurement and engineering teams specify the correct security layer, the table below compares the key attributes of these seven industrial printing techniques.
| Technique | Type (Overt/Covert) | Key Benefit | Difficulty in Replicating | Ideal Industry Use |
|---|---|---|---|---|
| Micro Text Printing | Covert | High-resolution authentication | Very High | Pharmaceuticals, Luxury |
| UV Invisible Ink | Covert | Hidden verification | High | Electronics, Pharma |
| Thermochromic Ink | Overt | Consumer interaction | High | Food, Cosmetics |
| Guilloche Patterns | Overt | Complex design security | Very High | Currency-style packaging |
| Variable Data Printing | Covert/Overt | Track & trace (QR code security) | Medium-High | All industries |
| Color Shifting Inks | Overt | Instant visual authentication | Very High | Luxury goods |
| Holographic Hot Stamping | Overt | Premium anti-copy feature | Extremely High | Electronics, Cosmetics |
Analyzing these parameters ensures that brands select the most cost-effective and secure technology for their specific product vulnerabilities.
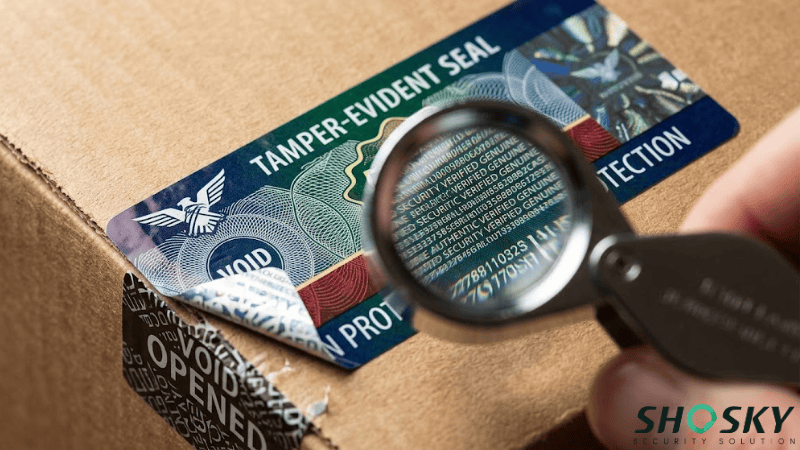
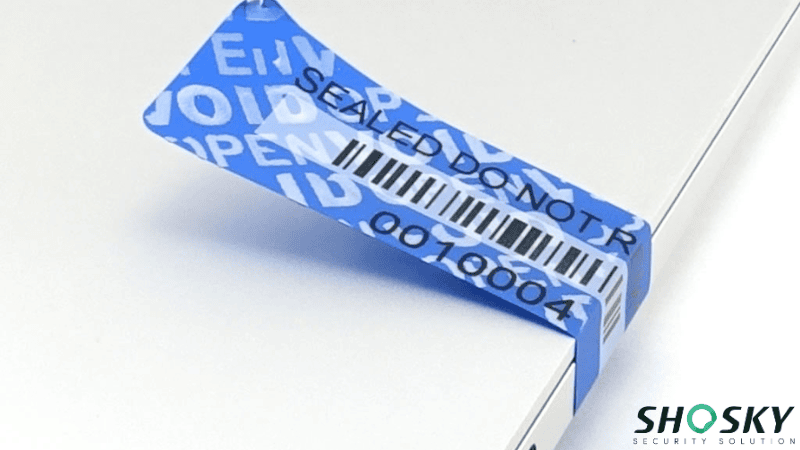
Integrating Security Printing with Tamper-Evident Materials
The most advanced security printing can be defeated by a single act, which is peeling off the label and gluing it to another place. Tamper-evident materials seal that gap completely. By printing the security inks and covert features onto substrates designed to self-destruct when removed, the label and its authentication data cannot be separated from the original packaging.
Integration of accurate security printing with tamper-evident engineering can provide protection to packaging on two fronts at once: what counterfeiters can observe but can never reverse.
- Total Transfer VOID Substrates: When peeled, the acrylic adhesive forcefully separates, imprinting a permanent “VOID” message directly onto the product housing.
- Destructible Vinyl Substrates: Engineered to be extremely brittle, this substrate fractures into microscopic fragments upon tampering, physically destroying the label.
By using this method, brands can develop an entire counterfeit prevention system of packaging that covers both visual and physical product security, and the outcome is a fully developed, multifaceted defense that is embedded in the package itself.
FAQs
Q1: What is the primary difference between overt and covert security features?
Overt features (like holograms and color-shifting inks) are visible to the naked eye for instant consumer verification. Covert features (like UV ink and microtext) are hidden and require specialized forensic tools for inspection by authorized personnel.
Q2: Can variable data printing (VDP) prevent mass counterfeiting?
Yes. By serializing each package with a unique QR code connected to a cloud database, any mass duplication of a single code will trigger instant anomaly alerts when scanned in the supply chain.
Q3: Why are thermochromic inks effective against counterfeiters?
The specialized industrial pigments required for temperature-reactive inks are heavily controlled by chemical manufacturers. This creates a supply chain lockout that severely limits counterfeiters’ access to the necessary raw materials.
Q4: How do tamper-evident materials enhance security printing?
They provide a necessary physical barrier. If a counterfeiter tries to peel a genuine security-printed label to place on a fake product, the tamper-evident substrate will permanently self-destruct, rendering the stolen label useless.
Fortify Your Supply Chain with Shosky Security Solutions
In a world where counterfeiters are getting more advanced, simple packaging is no longer sufficient. A multi-layered strategy encompassing both overt and covert security printing and tamper-evident materials is a complete defense against fraud.
Micro text and UV inks, QR code security, and security holograms all can be important additions to your anti-counterfeit packaging strategy. It is not about implementing a single solution but creating a system that collaborates to defend your brand everywhere.
Shosky Security engineers advanced brand protection solutions tailored to your strict compliance requirements. Contact us today to implement cutting-edge counterfeit packaging prevention and secure your global brand equity.